CLASSIFIED MEMORANDUM
Clearance Level: BLACK VEIL
Distribution: Compartmentalized / Eyes Only
Subject: Fragmentation of State Authority Under Pressure from Transnational Illicit Networks
Summary
This memorandum consolidates intelligence regarding the emergence of highly organized transnational criminal structures operating parallel to, and in some cases within, legitimate state systems. These entities exhibit characteristics of decentralized command, ideological fluidity, and economic motivation driven by untraceable capital accumulation.
Estimated scale of illicit financial flow: multi-trillion USD annually, derived primarily from narcotics distribution, human exploitation markets, and auxiliary shadow economies.
Operational Doctrine of Networks
Recovered intelligence suggests these networks are not merely profit-driven, but strategically oriented toward system destabilization. Their methods include:
- Systematic erosion of public trust in institutions
- Psychological warfare targeting law enforcement morale
- Co-option and infiltration of political and security structures
- Creation of high-impact, high-visibility crime events designed to overwhelm investigative capacity
These operations are calibrated to produce fear, confusion, and institutional fatigue rather than simple concealment.
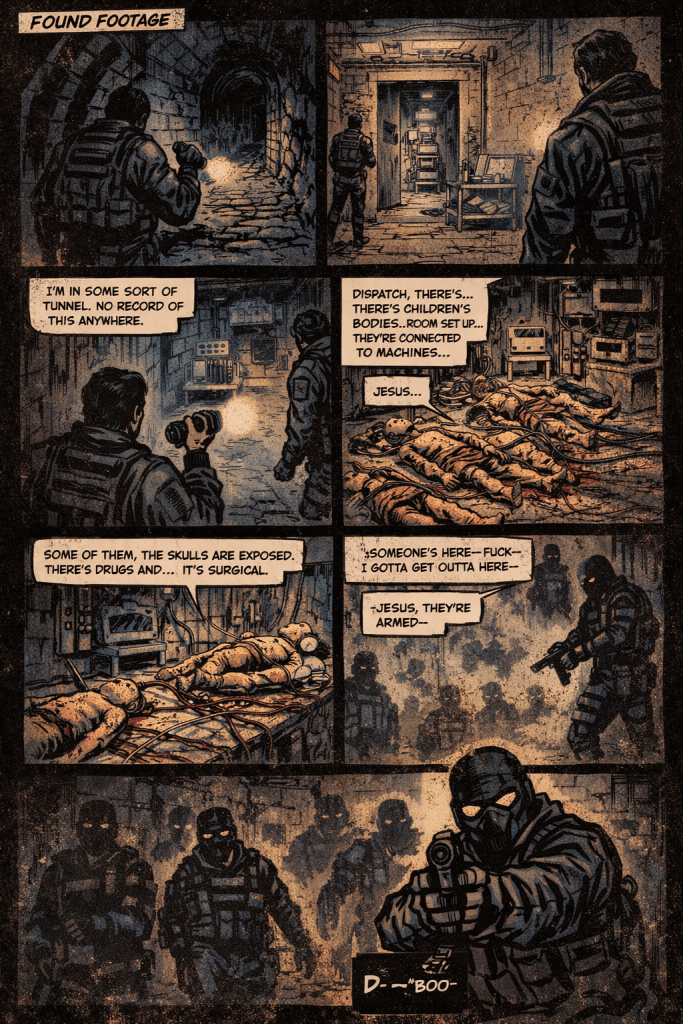
Psychological Warfare Tactics
Field reports indicate deliberate staging of extreme crime environments intended to:
- Overload investigative personnel
- Trigger long-term trauma responses among first responders
- Accelerate attrition within police and forensic units
- Lower institutional experience thresholds as veteran officers exit
This results in a feedback loop:
Less experienced investigators → higher psychological vulnerability → reduced investigative effectiveness → increased operational freedom for networks
Recruitment and Control Structures
Networks reportedly draw from:
- Former prison populations with specialized skill sets
- Individuals with demonstrated antisocial resilience
- Displaced operatives from historical conflict zones
Control is maintained through:
- Financial dependency
- Coercion and blackmail
- Familial leverage against political or institutional figures
The structure resembles a shadow governance layer, capable of exerting influence across jurisdictions.
Historical Continuity
Patterns observed align with post-conflict black market expansions seen after major geopolitical events. Intelligence suggests that:
- Wartime logistics routes evolved into peacetime trafficking corridors
- Financial pipelines established during conflict persisted and scaled
- Personnel networks transitioned from ideological warfare to profit-driven operations
These legacy systems now underpin modern illicit economies.
Parallel Conflict Environment
Analysts characterize the current state as a low-visibility, high-intensity shadow conflict, involving:
- Competing criminal factions
- Embedded corruption nodes within institutions
- Selective targeting of investigative or reform-oriented actors
This conflict is largely invisible to the general population, yet shapes systemic instability.
Information Leakage and Public Awareness
Recent high-profile criminal cases and investigative disclosures have increased public awareness of elite-level exploitation and corruption networks. However:
- Information remains fragmented
- Narratives are often diluted or contested
- Full structural visibility is obscured
This creates a paradox where the public is aware of symptoms but not the system.
Primary Objective of Networks
All intelligence converges on a single unifying driver:
Maximization of untraceable capital to enable sustained autonomy from state control
Secondary effects include:
- Institutional corruption
- Social fragmentation
- Cyclical destabilization followed by normalization
Assessment
These networks do not seek overt control. Instead, they aim to:
- Weaken resistance
- Normalize dysfunction
- Operate indefinitely within systemic blind spots
The result is not collapse—but managed decay, in which authority exists, but effectiveness erodes.
End of Memorandum
Classification Remains Active


Hozzászólás